Capabilities
-
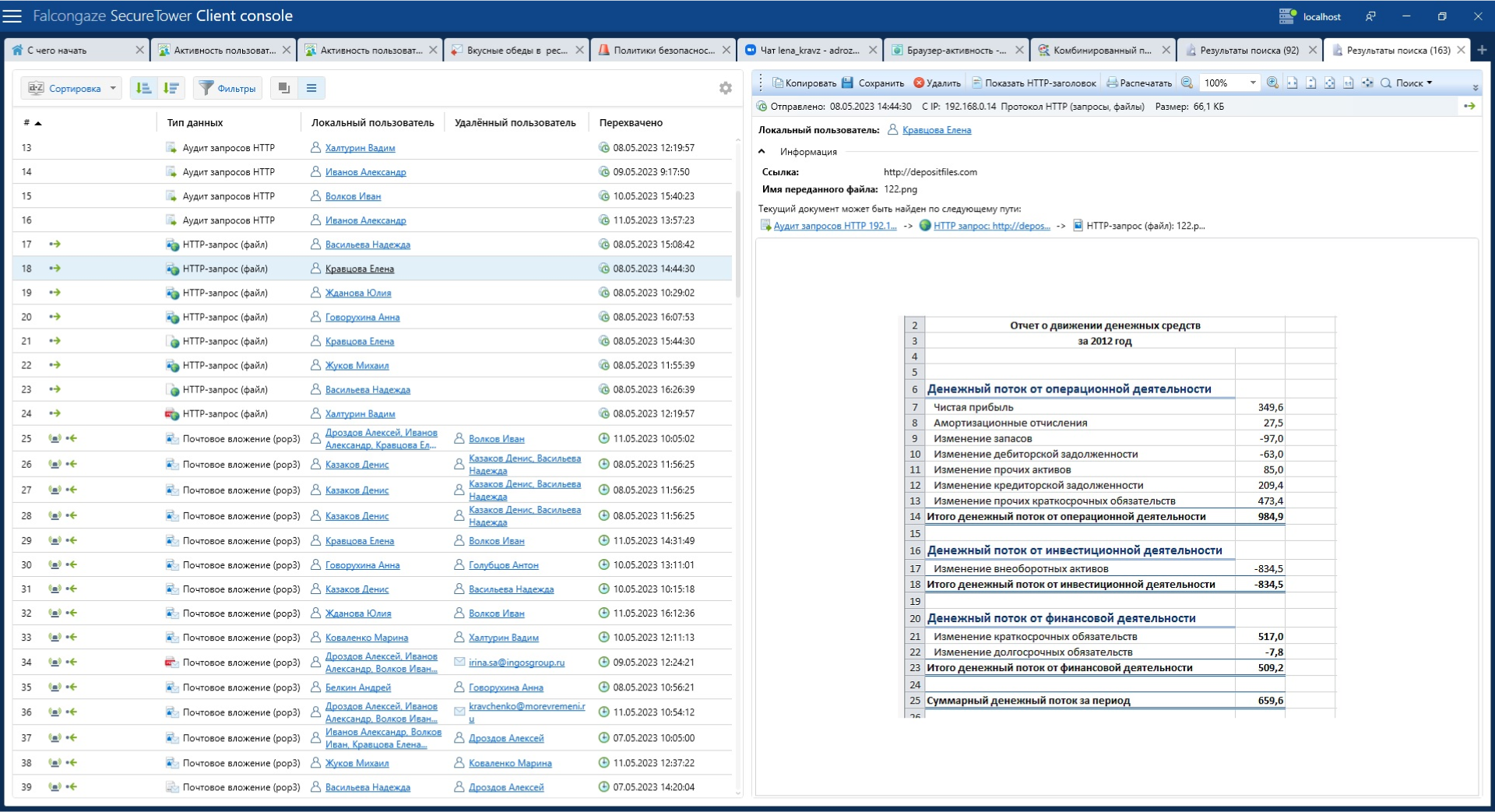
Detection of:
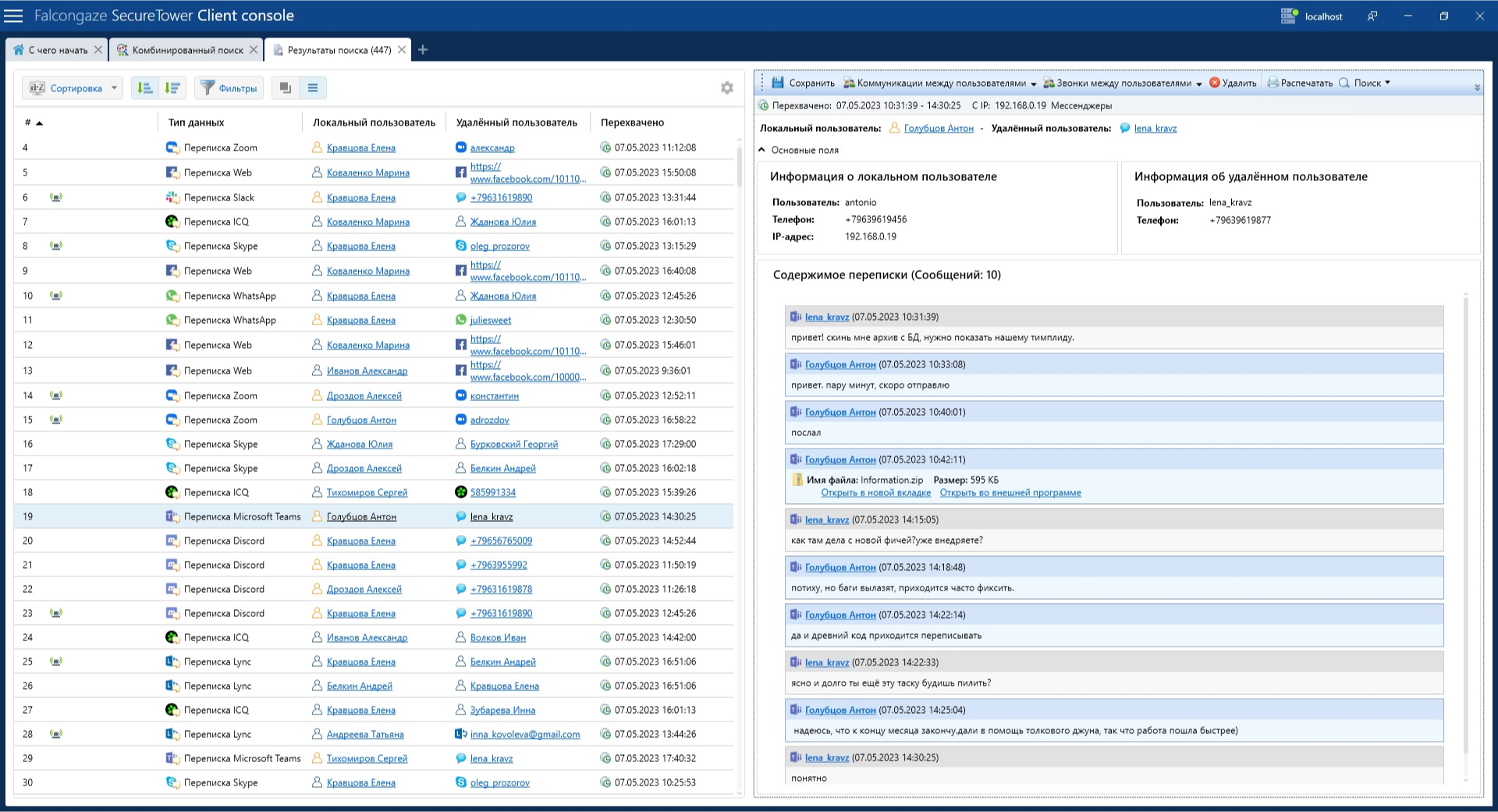
- onfidential information leaks
- internal fraud schemes
- insider activity
- inefficient employees
-
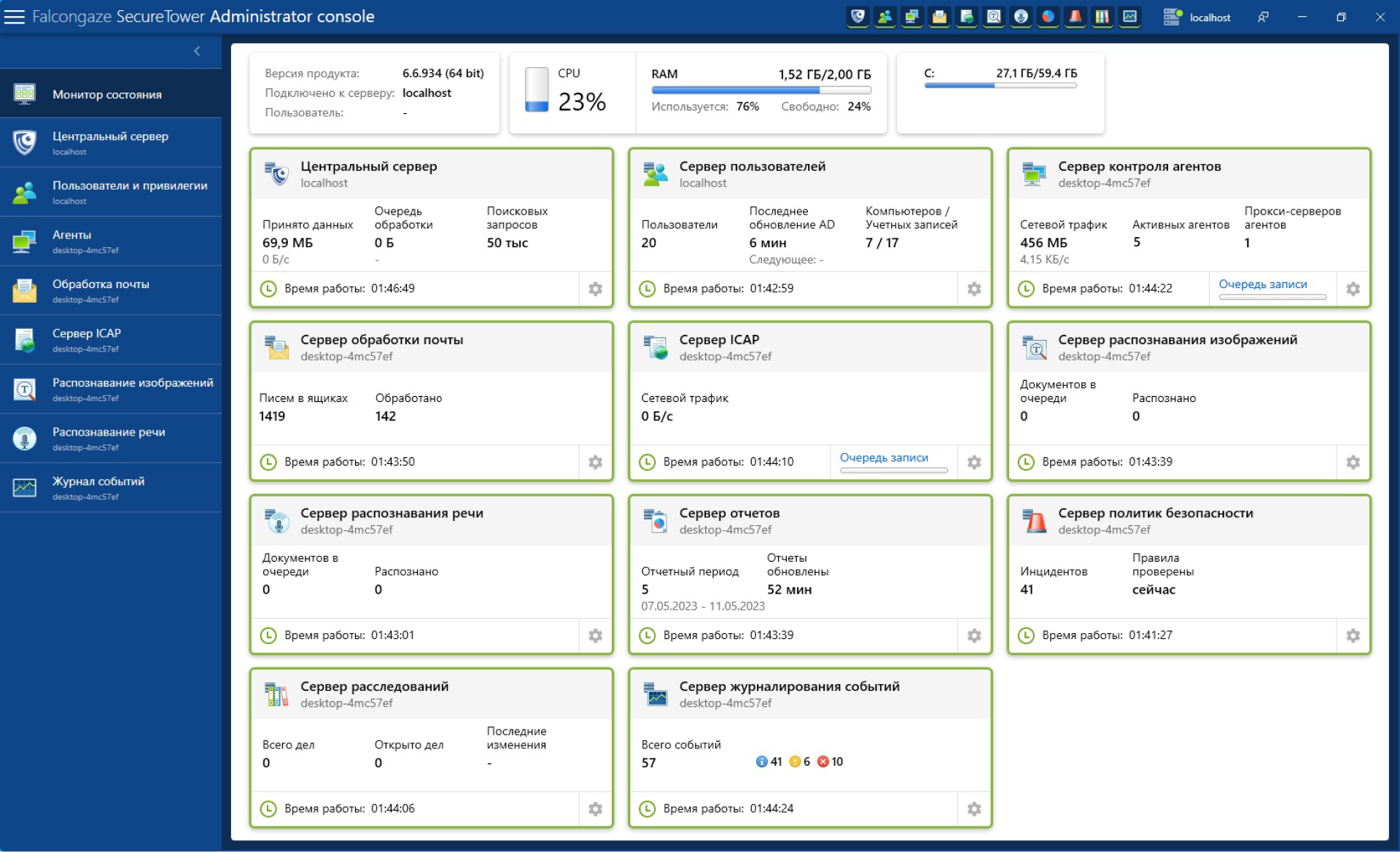
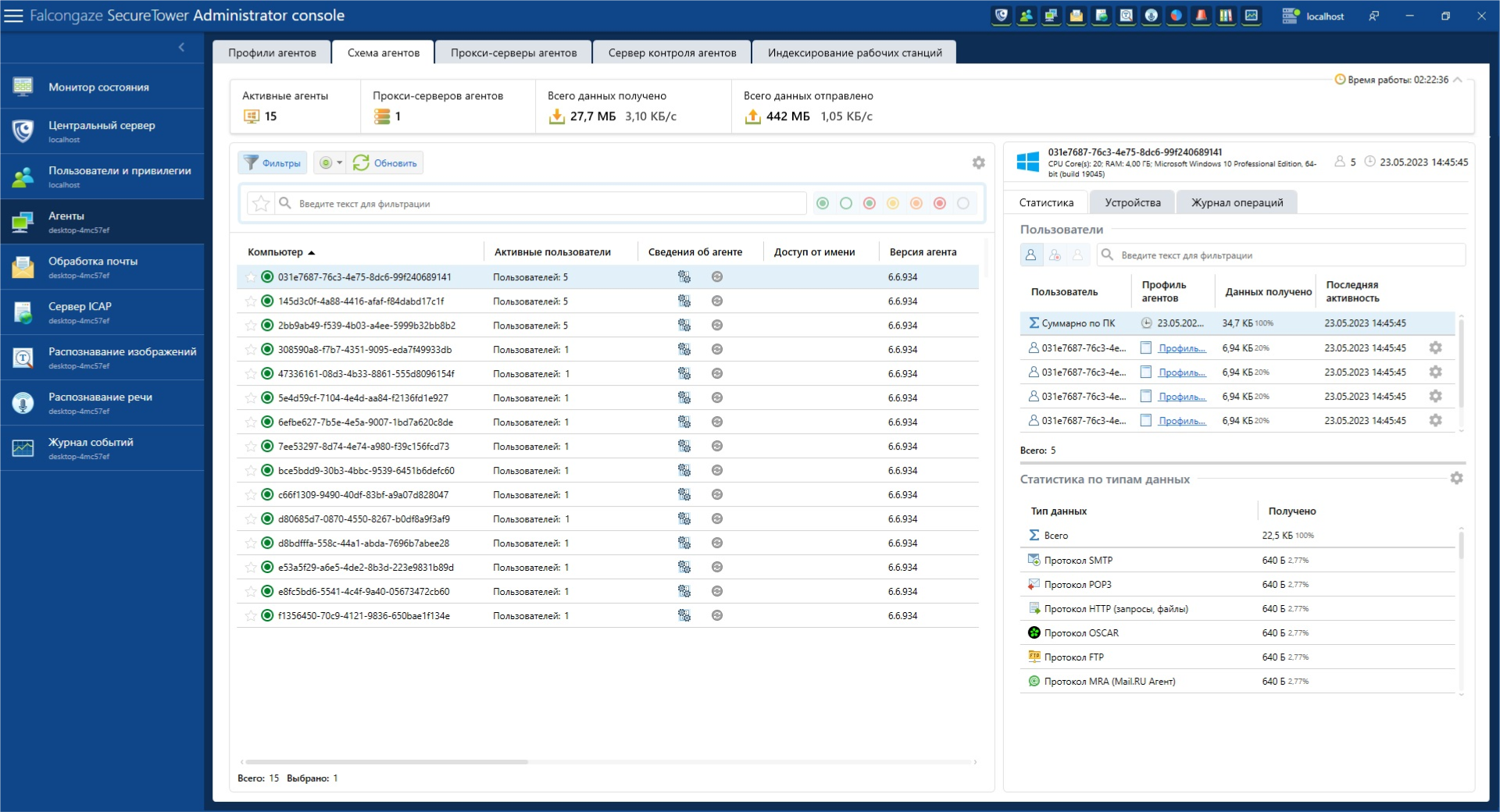
Monitoring of:
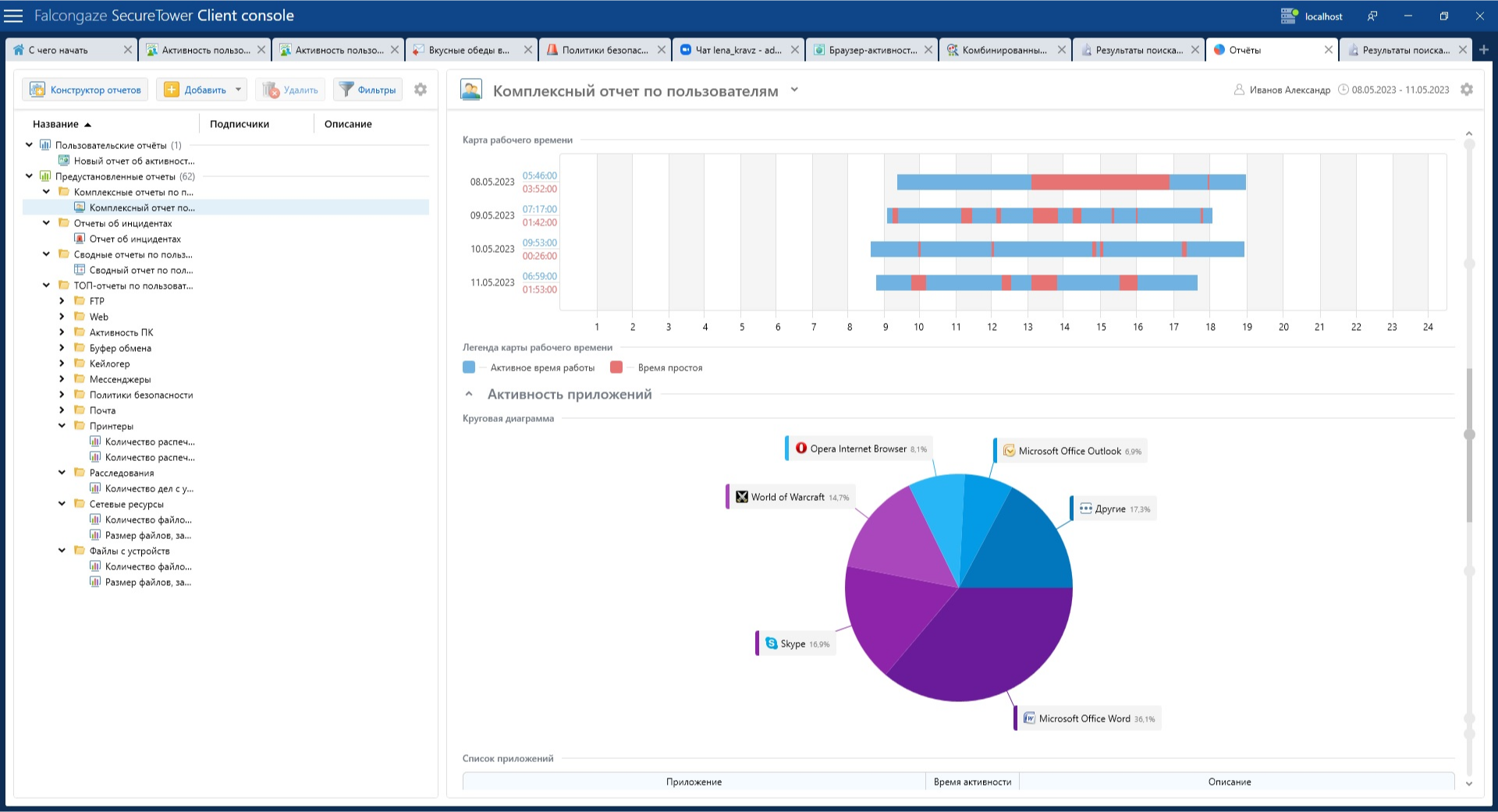
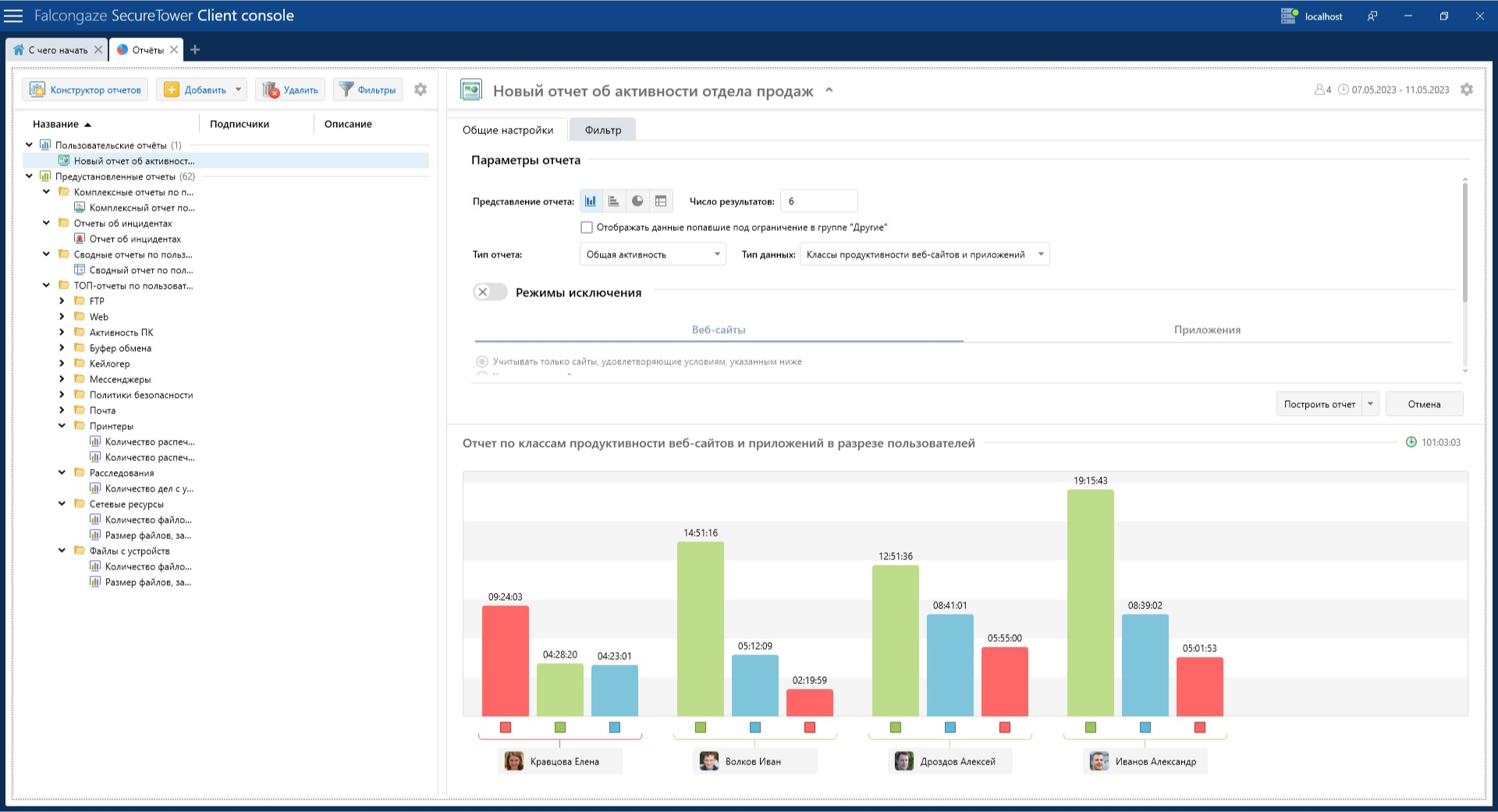
- employee activity on workplace computers
- staff efficiency and loyalty
- employee communications
- data transmission channels
-
Blocking of:
- malicious employee actions
- access to web resources, including by category
- application launches, including by category
- data copying to the clipboard
- USB device connections
-
Analysis of:
- the content of transferred files, including text, images, and audio
- employee work efficiency
- employee activity for potential risks
- employee performance statistics
-
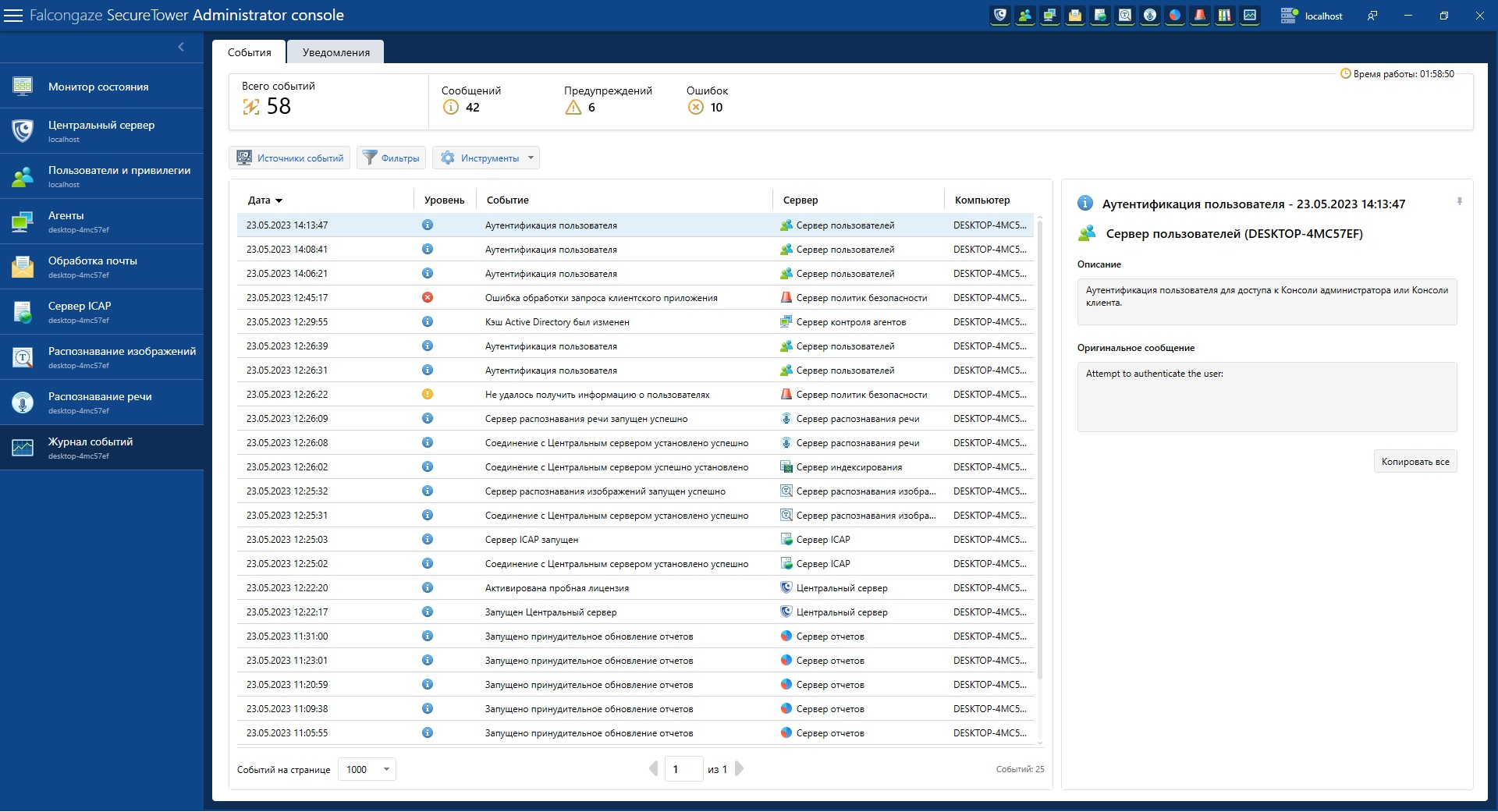
Investigation of:
- information security incidents
- causes of security policy violations
- causes of employee inefficiency
- internal fraud schemes