Capabilities
-
Automatic Discovery
Automatic discovery of current IT assets, applications, and services, including IPv6, virtual, and cloud components. The collected information can be easily integrated with third-party IT inventory systems such as Active Directory (AD), LDAP, and VMware vCenter. Administrators can easily organize and dynamically update IT assets in logical groups created based on dozens of criteria related to discovered hardware and software assets.
-
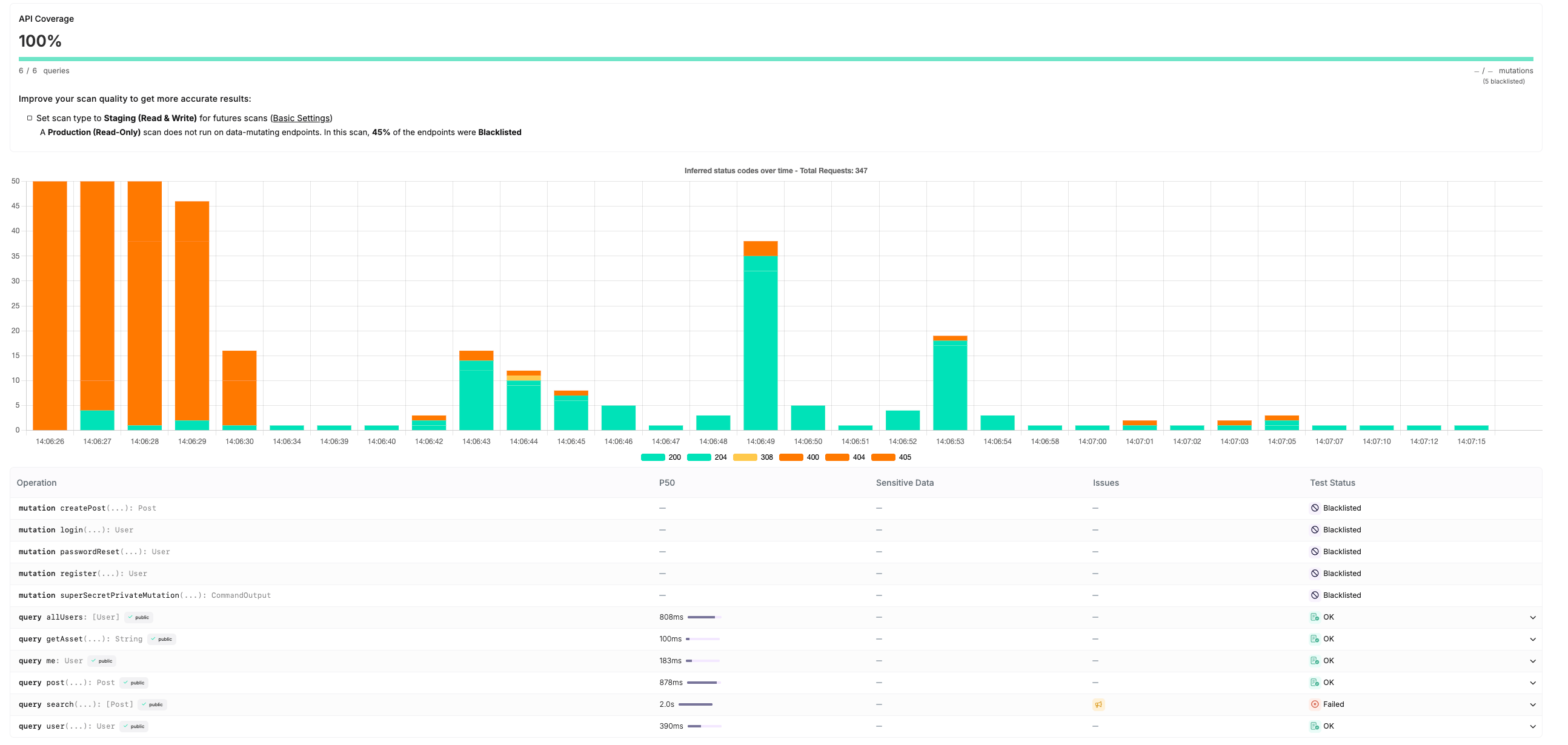
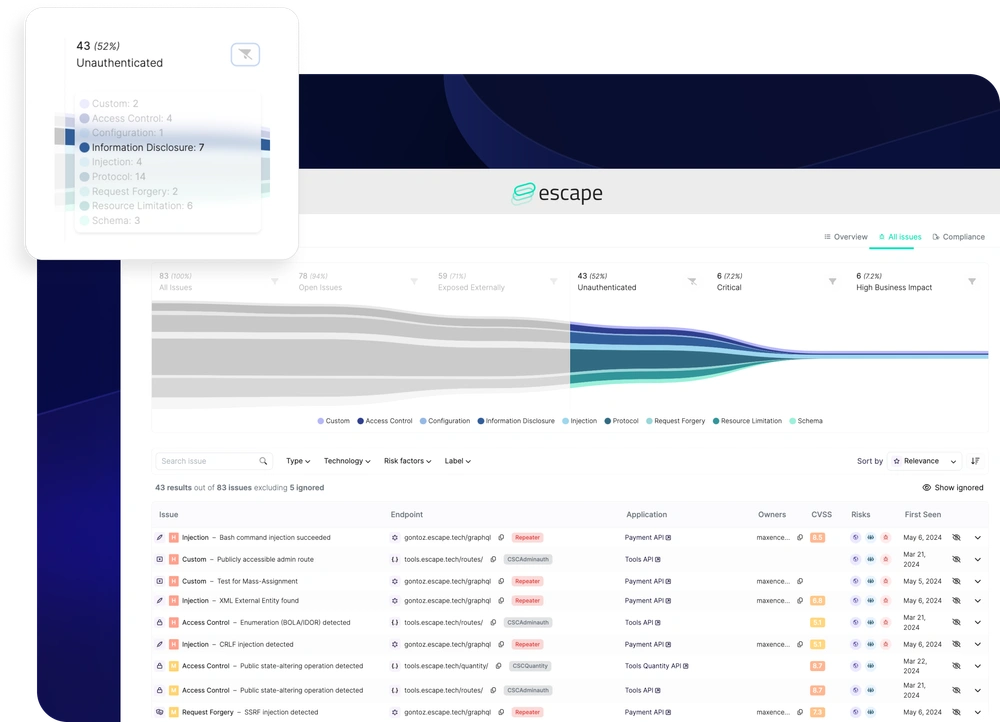
Deep network scanning and threat assessment
Comprehensive network scanning and assessment of threats such as vulnerabilities, misconfigurations, security policy violations, exposure to exploits and malware across all IT assets, including operating systems, networks, databases, and web applications.
-
Use of industry-standard risk prioritization frameworks
Use of industry-standard risk prioritization frameworks, such as the CVSS risk scoring system, to determine the severity of identified vulnerabilities. Threats can be filtered across 145 categories, enabling more effective prioritization of risk remediation within the IT infrastructure.
-
Automation of network scanning and report generation
Automation of network scanning and report generation allows these processes to be scheduled at times convenient for the administrator. The system also supports excluding specific vulnerabilities from reports, creating exceptions, and overriding corporate security policies for network scanning and reporting procedures, among other functions. Detailed reports are generated with recommendations for mitigating risks, including vulnerabilities and misconfigurations, so IT specialists can address identified issues promptly. The system offers a wide range of report templates, including reports designed to track changes over time.
-
Integration with Metasploit (penetration testing)
Integration with Metasploit for comprehensive assessment of identified vulnerabilities. Metasploit uses data collected by Nexpose or InsightVM vulnerability scanners to identify the most likely targets and potential attack paths.
-
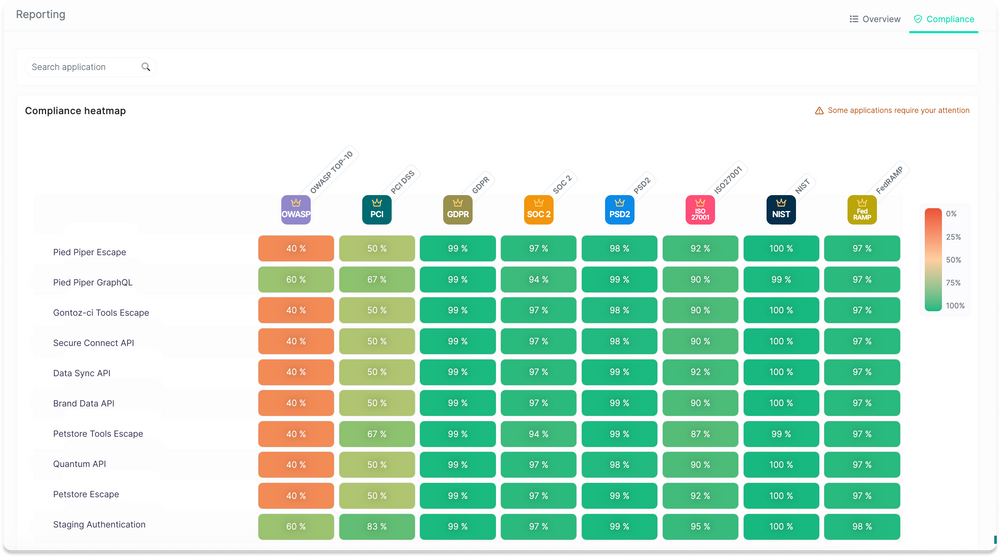
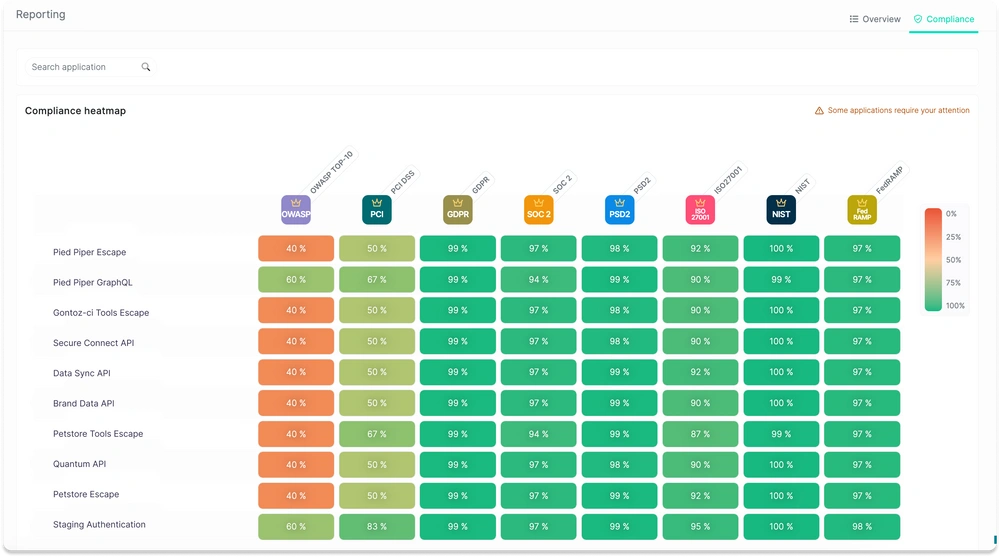
Monitoring internal security policies and compliance with standards
Monitoring internal security policies and comparing them against globally recognized standards such as FDCC and USGCB. Creation of custom security policies using the built-in Nexpose editor, along with security assessment and report generation in accordance with PCI, HIPAA, NERC, FISMA, SANS Top 20, and local regulatory requirements.
-
Automatic identification of virtual asset status and virtual network scanning
Automatic identification of the status of virtual assets and continuous scanning of the virtual environment, including guest operating systems, hypervisors, and virtual applications, for vulnerabilities. Integration with VMware vCenter is available to track changes within a dynamic virtual infrastructure.
-
Deploying a vulnerability scanner in minutes
Flexible and scalable deployment of a vulnerability scanner in just a few minutes, with the ability to choose deployment options across software, hardware, virtual, and cloud platforms, depending on the edition.